Operational Blind Spots: The Hidden Cost of Incomplete IT Coverage
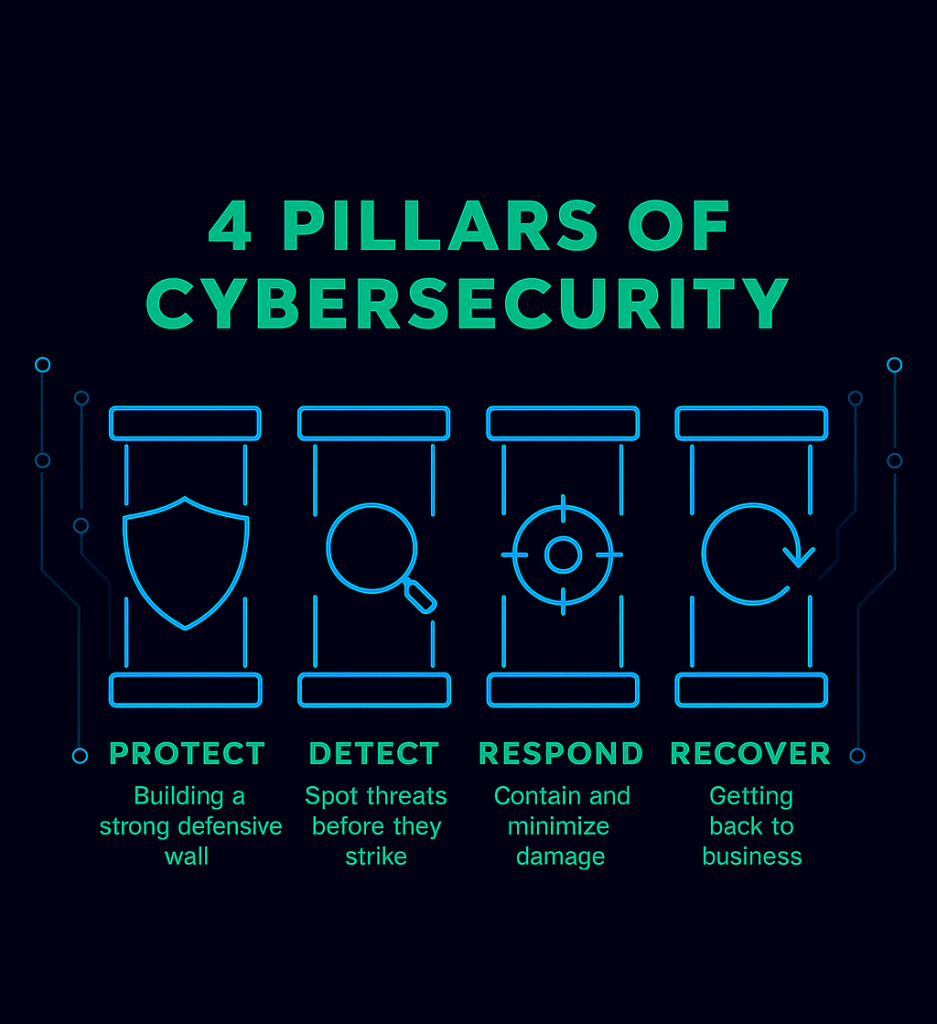
While meeting with a prospective client to discuss DCS’ Virtual Information Officer program, we reviewed the foundational cybersecurity pillars: Protect, Detect, Respond, and Recover. During that conversation, the client revealed a recent breach caused by an unpatched network appliance.
The MSP stated the device wasn’t included in their contract. The internal IT manager hadn’t validated the agreement or monitored the appliance. This created an operational blind spot — and attackers exploited it.
The client believed the MSP was solely at fault, but the reality is more complex. Cybersecurity breaks down when governance breaks down. Without clear accountability, even mature environments become vulnerable.
What this breach reinforces
- Assumptions create risk, especially around “who owns what.”
- MSP contracts define boundaries, not full protection.
- – Unmanaged or unpatched devices become open doors.
Executive Recommendations
- Establish governance over all IT assets — Leadership should require visibility into what exists, who owns it, and how it’s maintained.
- Align contracts with operational reality — MSP agreements must be mapped to actual infrastructure, not assumptions.
- Implement risk‑based patching — Appliances and edge devices should be prioritized, not overlooked.
- Adopt a strategic oversight function — A Virtual Information Officer ensures alignment between business goals, IT operations, and security controls.
- Conduct post‑incident reviews — Not to assign blame, but to strengthen processes and eliminate ambiguity.
A trusted advisor doesn’t just help you respond to incidents — they help you prevent the ones caused by unclear ownership and unmanaged risk.
